privacy
privacy — my Raindrop.io articles

The platform has become a core technology around the world, relied on by governments and extended families alike, Sam Knight writes. What are we all doing there?

Inside the world of extreme-privacy consultants, who, for the right fee, will make you and your personal information very hard to find
How a privacy researcher proved a politician wrong, and how she created the first ever definition of anonymity in the process.
A new attribution approach uses large sets of anonymized data to infer which channels and campaigns led to conversions.

A story of secrecy, resistance, and the fight for digital freedom.

Summarizing and explaining the 18 rules for HIPAA Safe Harbor (and the so-called 19th rule). What are the rules and their rationale? Alternative to Safe Harbor.

Brave Search, the browser developer's privacy-centric Internet search engine, is celebrating its first anniversary after surpassing 2.5 billion queries and seeing almost 5,000% growth in a year.
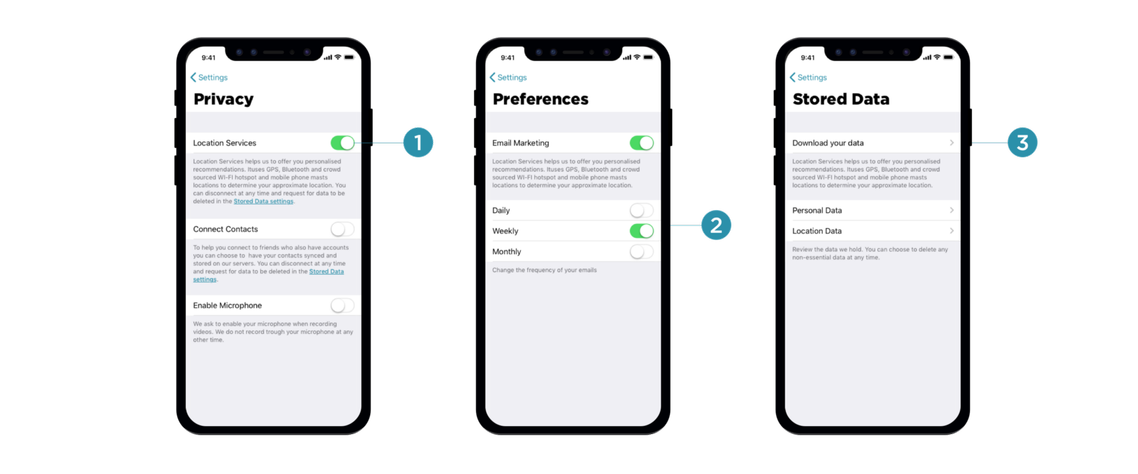
Many mobile applications require access to location, photos, and even the camera during installation, which isn’t something most customers would be happy to consent to. In this series of articles, Vitaly Friedman talks about privacy-related design patterns. You’ll be exploring some of the respectful ways to approach privacy and data collection, and how to deal with the notorious cookie consent prompts, intrusive push notifications, glorious permission requests, malicious third-party tracking and offboarding experience.
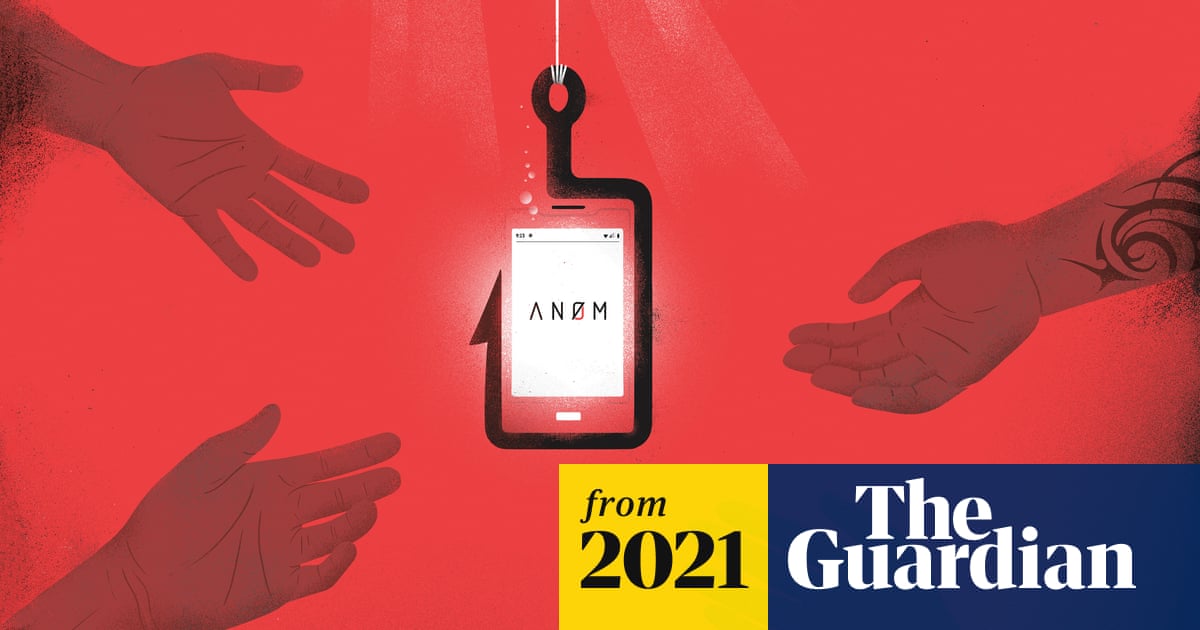
Billed as the most secure phone on the planet, An0m became a viral sensation in the underworld. There was just one problem for anyone using it for criminal means: it was run by the police